We are considering transitioning from another backend service for our web app. As the app grows, it’s becoming more difficult to manage security and building new modules due to a lack of robust security features.
I have a few questions that I have not been able to figure out from the videos or missions. I hope this is the right place to ask… if not, just let me know.
How do we handle setting up the security for object level roles? For example:
Users = {id, name, role}
Project = { Id, name, commission, dueDate }
UsersToProjects = { id, person, project, role, lastAccessed }
Two possible choices for UsersToProjects.role are Project-Manager and Contractor.
Project-Manager can CRUD all fields in their Projects.
Contractor can view Project.name and Project.dueDate
Anonymous users can view any Project.name and create projects assigned to a user
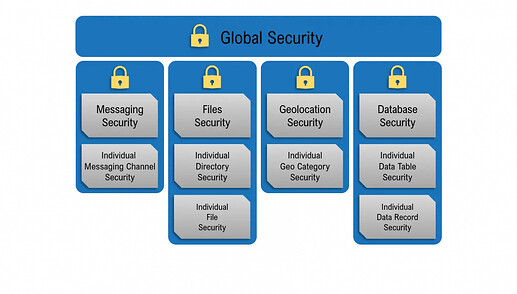
I understand the global roles, But how do we handle these types of row/column level roles for individual objects?
I’m asking specifically about how to handle the security setup. I understand how to get the data and sql, but want to make sure for instance that a contractor never knows the commission of a project they are assigned to. But that same contractor could be a project manager on another project.